A Security Breach with Potentially Devastating Consequences
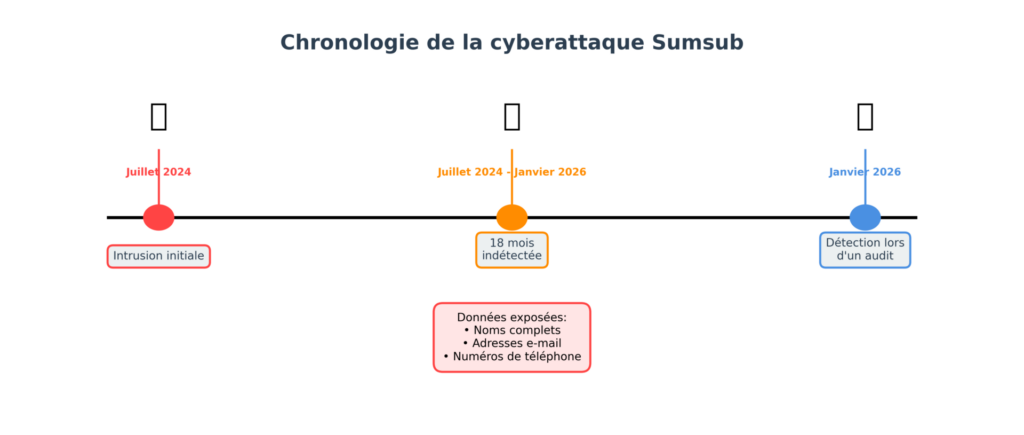
In early February 2026, Sumsub, one of the world’s leading online identity verification providers, disclosed that it had fallen victim to a cyberattack dating back to July 2024. This intrusion, which went undetected for 18 months, was only discovered in January 2026 during an in-depth security audit. The attacker exploited a malicious attachment sent through a third-party support ticket management platform to gain unauthorized access to an internal environment linked to customer support.
While the company claims that no identity documents, biometric data, or banking information were leaked, sensitive personal data was exposed: full names, email addresses, and phone numbers of an as-yet undetermined number of clients. For now, the exact scope of this breach and the number of affected individuals remain unclear.
This breach could affect users of numerous cryptocurrency exchange platforms that rely on Sumsub’s services for their KYC (Know Your Customer) verifications, including Bitget, Bybit, MoonPay, Bitpanda, Wirex, BingX, MEXC, Huobi, and Coinlist. Sumsub claims over 4,000 clients worldwide, and its solutions cater to a broad range of players: neobanks, crypto platforms, online brokers, and gambling platforms.
A Systemic Problem: The Weak Link in the KYC Chain
This case highlights a structural vulnerability in the KYC system. Know Your Customer verifications, although often criticized for the massive data collection they entail, cannot be performed by the platforms themselves but must be carried out through authorized third-party providers. This legal constraint creates a dangerous paradox: not only does it transfer risk beyond the exchanges’ control, but more importantly, in the event of a problem, multiple ecosystem participants can be simultaneously affected if they share the same service provider.
By concentrating such considerable volumes of sensitive data, providers like Sumsub become prime targets for cybercriminals seeking complete profiles to resell or exploit in sophisticated fraud schemes. The sector had already been alerted in 2025 following an incident involving a third-party integrator, underscoring the sensitivity of API configurations and the growing exposure to complex attacks combining technical vulnerabilities and exploitation of third parties.
Identity Theft: A Rapidly Escalating Scourge
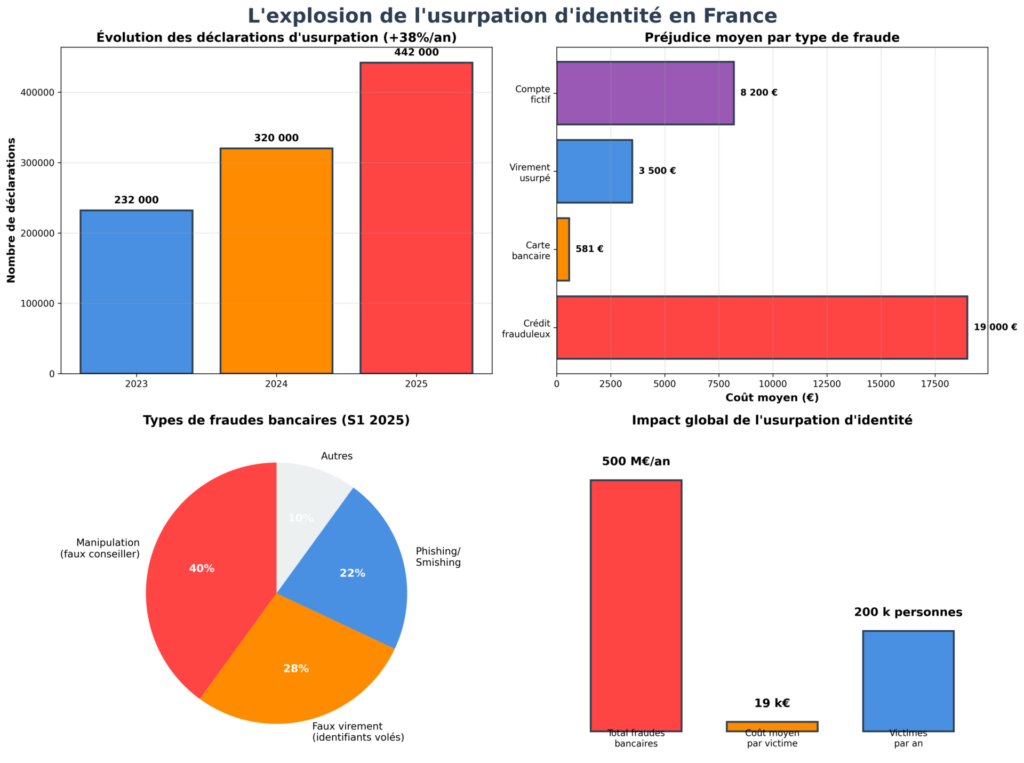
What makes this breach particularly alarming is that it occurs against a backdrop of an unprecedented surge in identity theft in France. The figures are staggering and point to a major crisis:
The scale of the phenomenon:
- At least 200,000 people fall victim to identity theft each year in France
- According to the SecuriNum Observatory, more than 320,000 identity theft reports were recorded last year, a 38% increase compared to 2023
- Between January 1 and 31, 2026 alone, more than 90 million accounts had their data leaked as a result of various security incidents
The financial cost:
- The losses are considerable: an average of 19,000 euros for fraudulent loans
- In total, banking and financial fraud is estimated to amount to at least 500 million euros per year
- Manipulation fraud (including fake bank advisor fraud) accounts for approximately 40% of the total value of fraud in the first half of 2025, up from 32% in 2023-2024
“Low-Sensitivity” Data? A Dangerously Misleading Shortcut
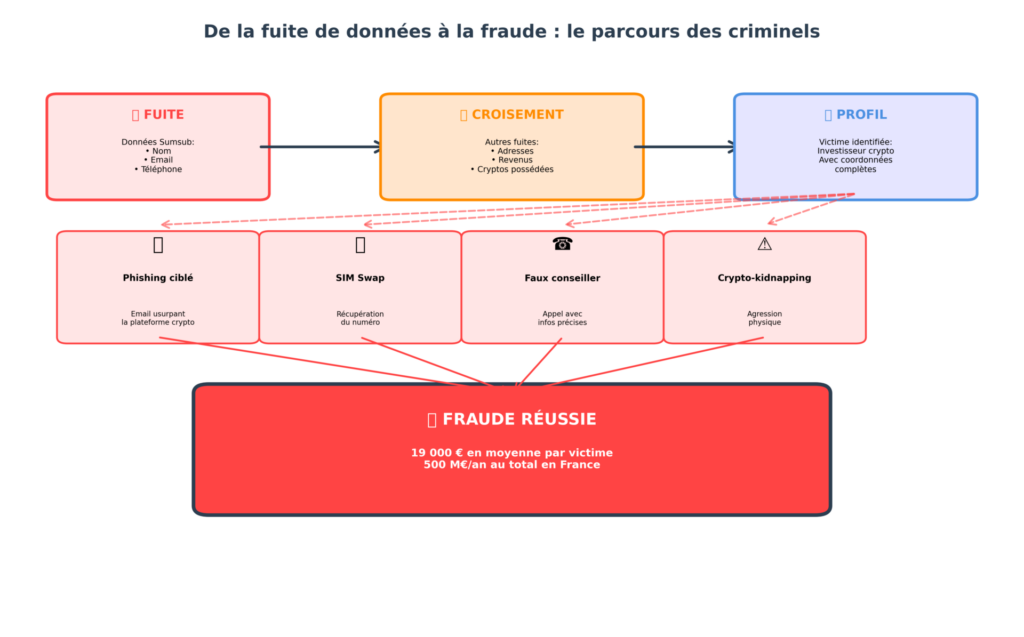
Sumsub seeks to reassure by stating that no “high-risk personal data” was compromised. However, this analysis dangerously minimizes the actual risks. Even without access to complete identity documents, the combination of a name, contact details, and a financial service can be enough to fuel highly effective targeted phishing and identity theft campaigns.
Techniques for exploiting stolen data:
- Ultra-targeted phishing: Knowing a person’s full name, email address, and the fact that they hold an account on a specific crypto platform, fraudsters can craft extremely credible phishing emails impersonating the platform in question.
- SIM swap attacks: An exposed phone number can be the target of a SIM swap attack, allowing criminals to intercept two-factor authentication codes and take control of banking and crypto accounts.
- Profile reconstruction: The real danger lies in the ability for malicious actors to cross-reference different compromised databases. As highlighted by Cryptoast, “it would be possible to obtain different compromised databases related to cryptocurrency to create a precise map of wealthy investors, using numerous personal details gathered from multiple sources.”
- Fake bank advisor fraud: Armed with precise personal information, fraudsters can impersonate bank advisors with greatly enhanced credibility. This form of fraud has surged, rising from 32% to 40% of total fraud by value.
The Modern Arsenal of Identity Theft
With the stolen data, the fraud possibilities are numerous and devastating. By recovering all personal data and contact information, criminals can:
- Take out fraudulent mortgages in the victims’ names
- Apply for consumer loans without the victim immediately noticing
- Set up shell companies to launder money or commit other offenses
- Divert wire transfers by impersonating legitimate suppliers
- Commit health insurance fraud or produce false tax notices
Fraudsters have become professionalized. Organized into micro-teams that recruit on Telegram or Discord, they gather, cross-reference, and assemble fragments of digital life until they reconstruct a fully exploitable identity. Artificial intelligence makes these attacks even more credible, as emphasized by the Banque de France in its priorities for 2025-2026.
Heightened Risk in the Crypto Ecosystem
For the cryptocurrency ecosystem, the risks are even more concerning. Since the beginning of 2025, there has been an alarming rise in “crypto-kidnappings”: individuals identified by their digital assets are being abducted and/or assaulted in order to extort their cryptocurrencies. Criminals sometimes even target family members.
As illustrated by a recent news report by Cryptoast: “We have your father, it’s about the crypto” — the son of a hostage held captive in Isere gave an exclusive account of this new form of crime directly linked to data breaches in the crypto sector.
The Sumsub breach provides criminals with exactly what they need: confirmation that certain individuals hold cryptocurrencies, along with their contact details. It is a dream map for targeting potentially wealthy victims.
An Alarming Trend: The Proliferation of Data Breaches
The Sumsub incident is unfortunately not an isolated case. Data breaches have become commonplace in France, with each day bringing new examples:
- O’Tacos: 29 million customer profiles compromised in January 2026
- Panorama Banques: 2.3 million profiles exposed
- French Volleyball Federation: approximately 1.2 million accounts affected
- URSSAF: nearly 12 million data records compromised
- National Assembly: personal data of members of parliament and staff leaked
- Several government ministries and public service portals hacked in recent weeks
These breaches can be caused by insufficient database security, but the threat can also come from within: several cases have revealed that malicious employees sell data or profiles of targeted individuals to criminal networks.
The KYC Regulation Paradox
The most absurd aspect of this situation is that KYC identification measures, designed to combat money laundering and terrorist financing, actually create new vulnerabilities. By requiring exchange platforms and online services to store sensitive data (identities, addresses, balances, etc.), regulators have inadvertently created prime targets for criminals.
When these databases are compromised — which is becoming increasingly frequent — the consequences far exceed simple identity theft. These measures often prove ineffective against fraud, which is frequently carried out through stolen accounts or nominees.
As a cybersecurity researcher noted on Twitter following the Sumsub incident: “This will reignite the debate around banning social media for children under 15, with this French trusted third party…” The irony is cruel: the companies meant to guarantee our digital identity are themselves becoming major points of failure.
Preventive Actions: Too Little, Too Late?
Faced with this alarming situation, authorities are multiplying their initiatives. The Observatory for the Security of Payment Instruments (OSMP) of the Banque de France has made the fight against identity theft on communication networks a priority area of work for 2025-2026.
Current or planned measures:
- Enhanced authentication: Deployment of the Number Authentication Mechanism (MAN) in late 2024/early 2025 to certify the number displayed when receiving a phone call
- IBAN verification: Implementation of a check for consistency between the IBAN and the wire transfer beneficiary’s name (October 2025) to combat IBAN fraud
- Remote payment security: Action plan to secure remote card payments outside 3-D Secure (MOTO payments)
- Digital identity solutions: Joint action with the digital and telecommunications sector
- Blocking fraudulent numbers: Mobilization of telecom operators to block calls made from numbers identified as intended only for receiving calls
- AI monitoring: Increased vigilance regarding the use of artificial intelligence and its impact on fraud
Essential recommendations:
Despite these technical measures, user vigilance remains indispensable. Denis Beau, Deputy Governor of the Banque de France and Chairman of the OSMP, emphasizes: “Strengthening the technologies ensuring payment security and implementing mechanisms to combat identity theft on communication networks are two pillars where significant progress has been made; but user vigilance remains indispensable.”
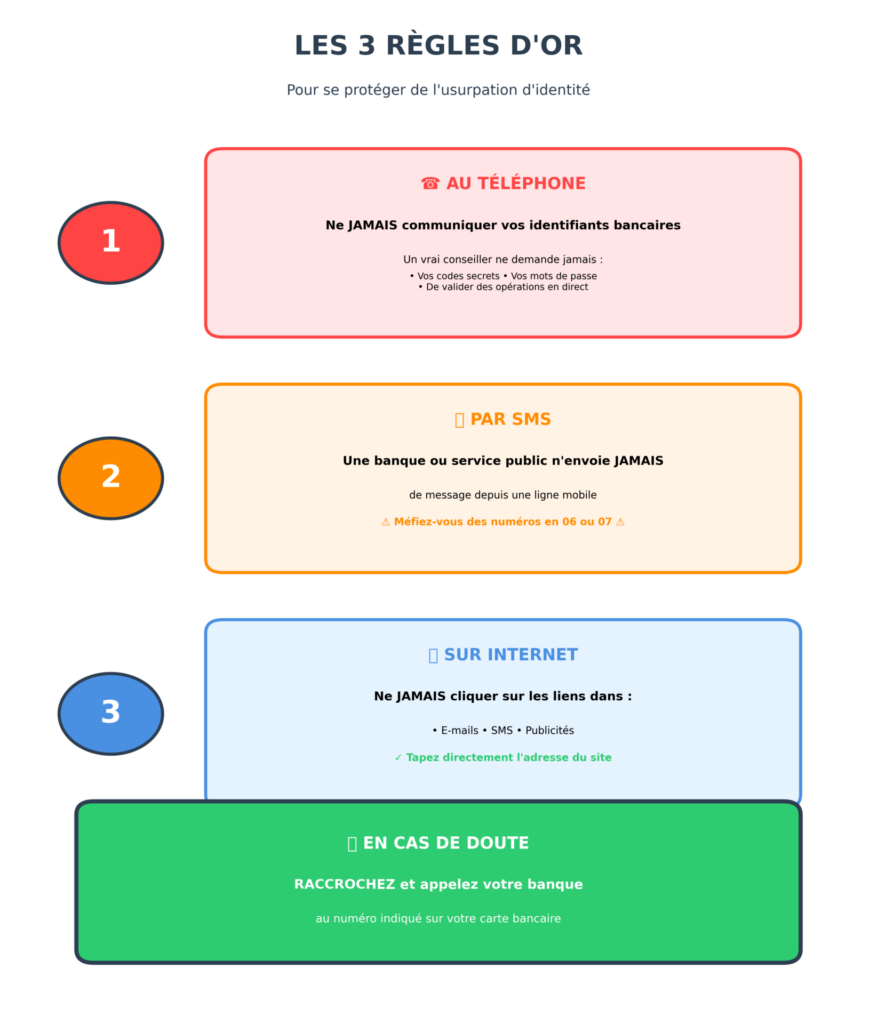
The three golden rules to follow:
- On the phone: Never share your banking credentials or validate transactions under the guidance of a supposed advisor. A real bank advisor never needs to ask for this information.
- By text message: A bank or public service never sends messages from a mobile number (06 or 07). Hang up as quickly as possible if you receive a call from a professional whose number you do not recognize.
- Online: Never use links contained in emails, text messages, or advertisements to access a website. Always navigate to websites by typing the address directly or using a link from a trusted source.
What to Do If You Are a Victim?
In the event of confirmed or suspected identity theft, here are the steps to take immediately:
- File a complaint: Go to any police station or gendarmerie. A complaint receipt is essential to trigger banking protections. The complaint can also be filed through the StopFraude online service.
- Contact your bank: Request enhanced monitoring of your account. Some banks activate a “fraud clause” that freezes suspicious transactions.
- Notify your insurer: Check whether your insurance covers identity theft.
- Report to government agencies: Tax authorities, health insurance, social benefits — notify them to prevent fraudulent reimbursements or unauthorized debits. FranceConnect accounts can be temporarily locked upon request.
- Do not neglect the psychological impact: The stress of identity theft can be significant. Some health insurance plans include psychological support sessions.
An Uncertain Future for Digital Security
The Sumsub case underscores a troubling reality: even digital identity guardians are not immune to vulnerabilities in their own subcontractors. The 18-month detection delay raises fundamental questions about the responsiveness of monitoring systems and the continuous oversight of access controls.
This situation perfectly illustrates the growing vulnerability of software supply chains. Ironically, this incident occurred just as Sumsub had published its annual report highlighting a 180% increase in sophisticated fraud in 2025.
For users of crypto platforms who used Sumsub for their KYC verification, vigilance is more critical than ever. It is recommended to:
- Be particularly vigilant against targeted phishing attempts
- Enable two-factor authentication on all accounts
- Closely monitor your banking and crypto accounts
- Never respond to unsolicited requests
- Consider changing your phone number and email address if possible
The increase in data breaches highlights the limitations of current anti-money laundering frameworks. By creating massive reservoirs of sensitive personal data, the KYC system has inadvertently built a risk infrastructure that benefits increasingly sophisticated organized criminals.
Until this fundamental contradiction is resolved, incidents like the Sumsub breach will continue to multiply, turning “trusted third parties” into vulnerabilities of trust. In this context, the question is no longer whether your data will one day be compromised, but when — and above all, how you will protect yourself when it inevitably happens.